Hello there,
Recently I've started to dig into the ORDS authentication and more specifically in how to make it work against my Oracle WebLogic server authenticators.
ORDS Service Definition
The first step is to create or define a REST service in our Oracle database. The oracle-base.com guys have a fantastic how to here. In summary you have to perform two operations:
- Enable the schema for REST
|
DECLARE ORDS.ENABLE_SCHEMA(p_enabled => TRUE, END; |
- Define the service
|
DECLARE ORDS.ENABLE_OBJECT(p_enabled => TRUE, END; |
In the above snippet we are exposing the table DEPLOYMENT for READ, UPDATE, INSERT and DELETE operations. For this example we are using the AutoREST feature of ORDS.
In my WebLogic side I have the ords listener application deployed against the /ords-sso context, and my Oracle Database is mapped against /devdb11. This means that I can access my service through: https://my.domain/ords-sso/devdb11/cerndb_mwctl_a_01_dev/deployment
ORDS configuration at a glance
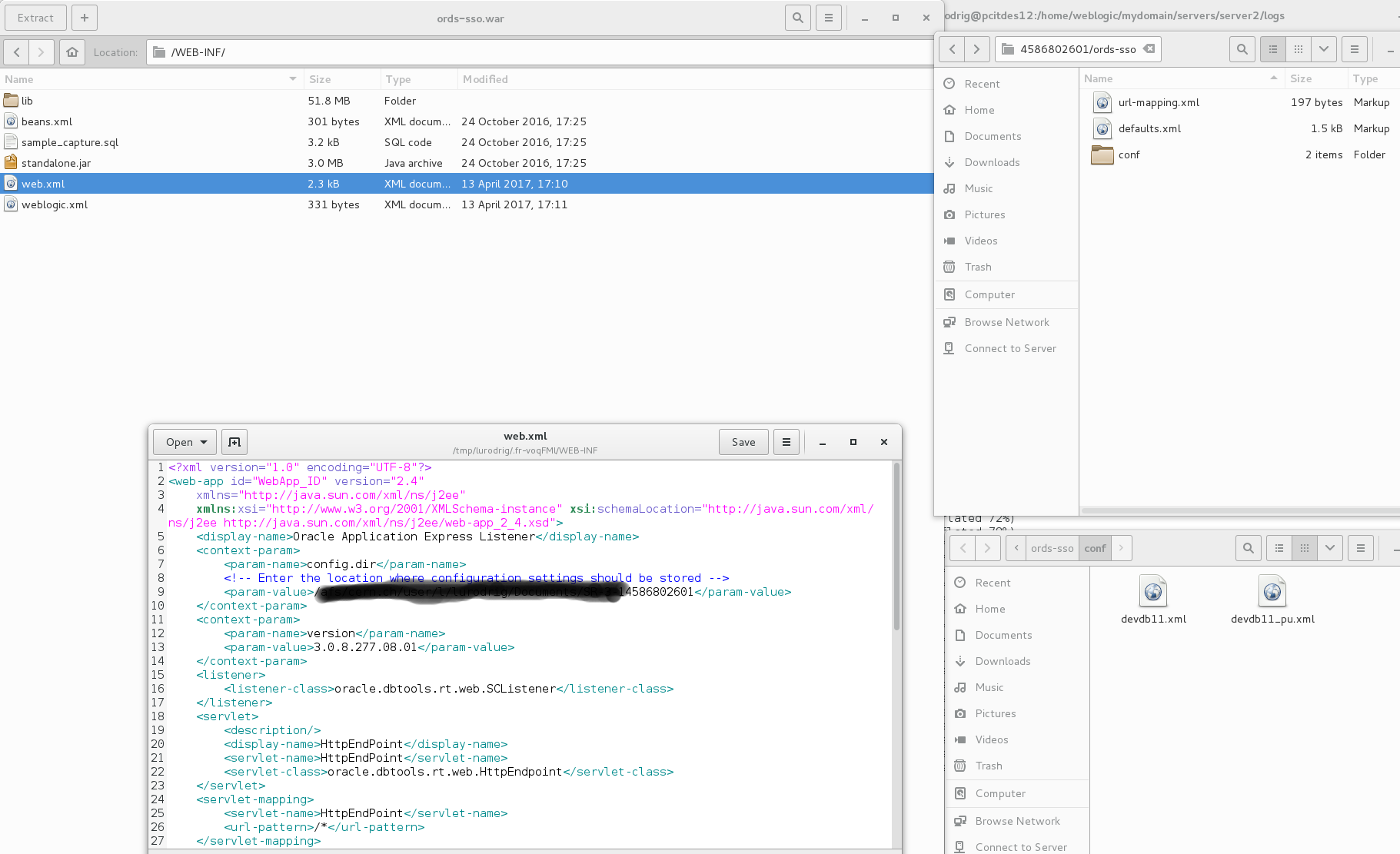
Although the aim of this post is not to show you how to setup your ords installation (for this you have great posts like this one from the smartdogservices.com people, thanks!) just have a quick look at the configuration files:
Protecting the ORDS Service
Now we want to protect our service. For this we need to:
- Define WHO can access:
| BEGIN ORDS.CREATE_ROLE('crud-deployments'); ORDS.CREATE_PRIVILEGE( p_name => 'crud-operations-on-deployment-table', p_role_name => 'crud-deployments', p_label => 'Deployment Data', p_description => 'CRUD operations on deployment table'); COMMIT; END; |
- Map the service URL:
| BEGIN ORDS.CREATE_PRIVILEGE_MAPPING( p_privilege_name => 'crud-operations-on-deployment-table', p_pattern => '/deployment/*'); COMMIT; END; |
If we now try to access our service we will get a "401 Unauthorized" and a link to the ORDS default sign-in form.
WebLogic and ORDS war SSO configuration
OK, we have everything set-up and ready, so now lets attack the real meat of this article, the SSO integration:
- Configure your managed server as a service provider. If the official documentation is not enough you can always have a look at Puneeth's blog entry here (thanks!)
- Configure your ords-sso.war. We want to protect the access to the /ords-sso application: when an unauthenticated request arrive WebLogic redirects it to our Identity Provider. As the authorization will be done by ORDS we allow all users to access:
|
<security-constraint>
<security-role> |
| <security-role-assignment> <role-name>AllUsers</role-name> <principal-name>users</principal-name> </security-role-assignment> |
- Install a credential mapper for your SAML2 Identity Asserter. This is needed by WebLogic in order to create the user Java Principals.
- Deploy your ords-sso war
You are done!
If now you try to access your service endpoint instead of being redirected to the default ORDS sign-in form you will be redirected to your IdP one. If you are curious about how weblogic manage this authentication you can enable this debug flags:
| -Dweblogic.DebugSecurityAtz=true -Dweblogic.DebugSecurityAtn=true -Dweblogic.log.StdoutSeverity=Debug -Dweblogic.log.RedirectStdoutToServerLogEnabled=true -Dweblogic.log.RedirectStderrToServerLogEnabled=true -Dweblogic.security.saml2.atn.DebugSecuritySAML2Atn=true -Dweblogic.debug.DebugSecuritySAML2CredMap=true -Dweblogic.debug.DebugSecuritySAML2Lib=true -Dweblogic.debug.DebugSecuritySAML2Service=true -Dweblogic.debug.DebugSecurityRoleMap=true |
Hope it helps and have a nice coding day!
Luis
